Redesigning ThreatConnect's Threat Graph
The Threat Graphs purpose was to allow cyber security analysts a way to visualize threat intelligence relationships for investigations, but the feature was experiencing a 60% decline in usage.
I successfully redesigned the core threat visualization experience, incorporating our AI/ML CAL data layer resulting in 73% monthly active usage, 40% reduction in investigation time, and $2.3M in prevented customer churn.
Field
Cyber Security
My Role
Product Strategy
UI/UX Design
User Interviews
Prototyping
Design Systems
Project Overview
The problem
ThreatConnect's Threat Graph was failing on multiple fronts: usage plummeted 60% over 18 months, putting 23% of enterprise customers at churn risk who cited poor visualization as a primary concern. Analysts abandoned the graph for third-party tools.
Through stake holder interviews and customer feedback analysis, I identified the following core issues:
1. Limited visibility: Graph confined to 25% of screen real estate, buried in tabs, which made it difficult to use.
2. No visual hierarchy: Impossible to distinguish between data types, relationships, or threat levels.
3. Missing context: No way to understand why two pieces of data were connected.
4. Workflow disruption: Couldn't save, share, or export data.
5. Poor performance: Slow loading times with large data sets.
"The current graph is cumbersome, time-consuming, and not helpful."
- Senior Threat Analyst, Fortune 500 Company
Before redesign
No way to save, edit or share
Difficult to view in a small area of screen
User must toggle between the small graph and a table view
Limited actions on data available
No way to hide or remove data from the graph
No enrichment are third party integration
Limited actions on data available
No way to tell what type of data or the relationships are
Single color categories make difficult to differentiate between data
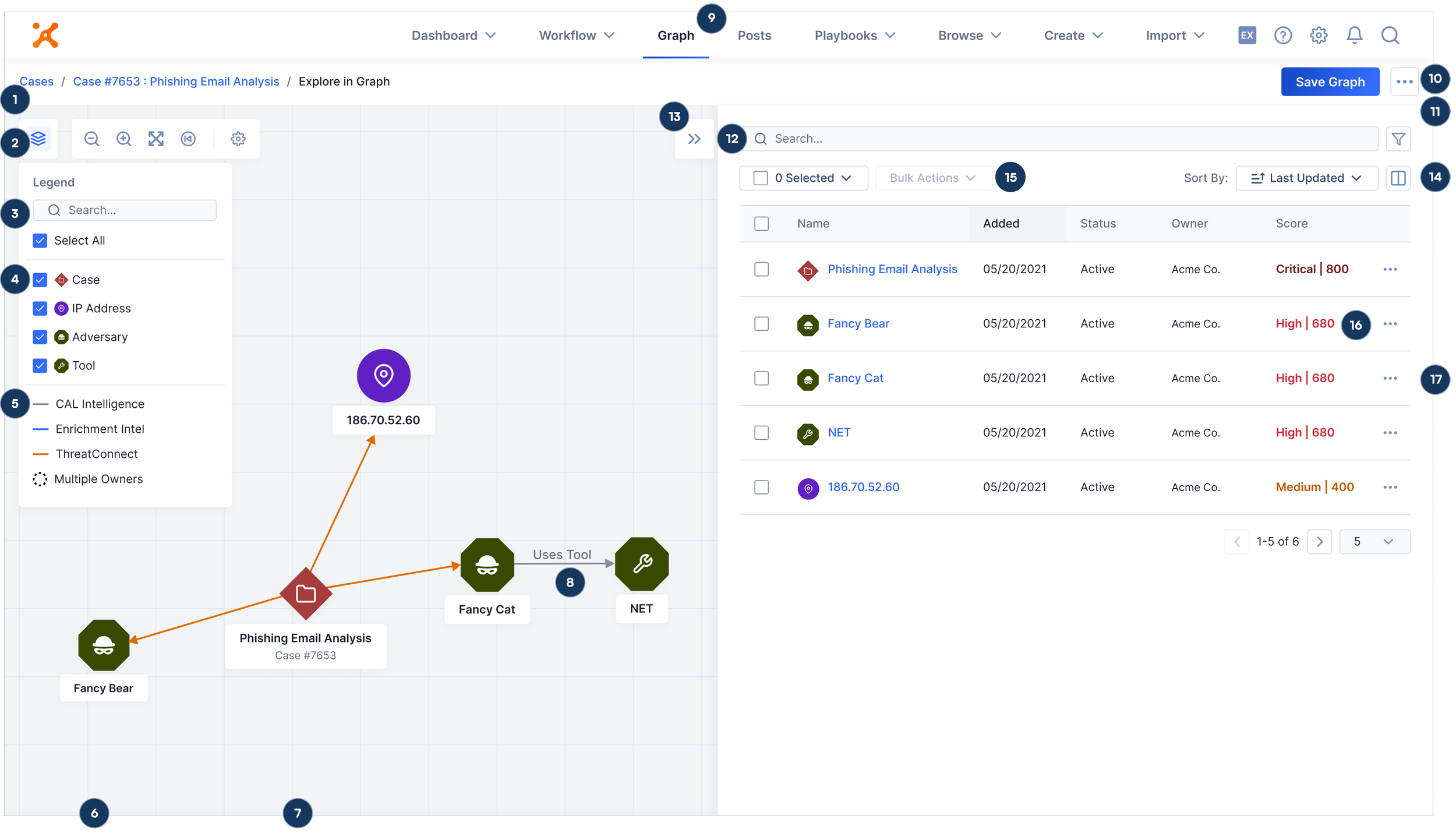
After redesign
Ability to access graph from anywhere in the platform
Graph controls grouped together for easy access
A searchable legend with custom data type icons
Ability to hide or show data types in the graph
New users quickly understand where data comes from
New pivoting allows running automations, using enrichments tools and adding associations
Ability to see cases on the graph and pivot from them
Context on how data is related shown on directional arrows
Top nav placement and area to see all saved graphs
Save and export capabilities
Full screen view of the graph
Search data in the table for larger data sets
Hide and or show table view while being able to pivot
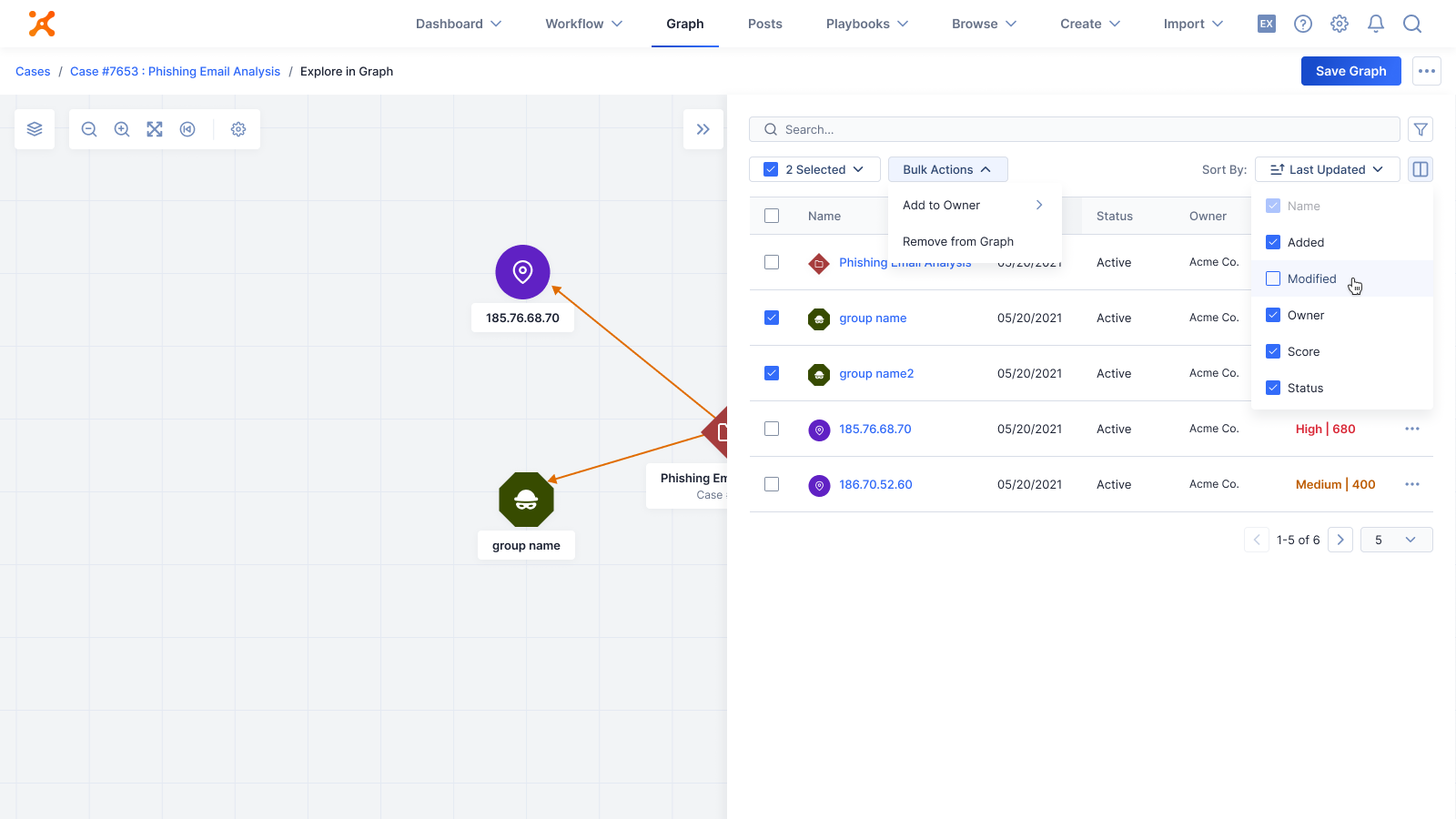
Users decide which data columns they see in the table view
Ability to select data and take bulk actions
Scoring provided by CAL AI/ML to better understand threats
Take actions on a single piece of data
Research and Discovery Phase
User research approach
I conducted in-depth interviews with internal analysts and Fortune 500 customer analysts, exploring investigation processes, pain points, and tool preferences, with findings tracked in Airtable.
To gain deeper insights into real-world usage, I conducted contextual inquiry sessions where I observed 6 live threat investigations, documenting current workflows, workarounds, and moments of friction that weren't captured in interviews alone.
Key insights
1. 78% of analysts prefer starting investigations visually.
2. 89% of investigations involve multiple analysts. They need a way to save, export, share, and comment on investigation graphs.
3. Investigations can last a week or even a month. The graph needs to evolve over time.
4. Analysts need to understand relationship confidence levels. Source attribution is crucial for data reliability. Connection to existing cases and incidents is required to visualize relationships.
5. Must handle 500+ indicators without performance degradation.
6. There is no way to take an action on an piece of intel when needed.
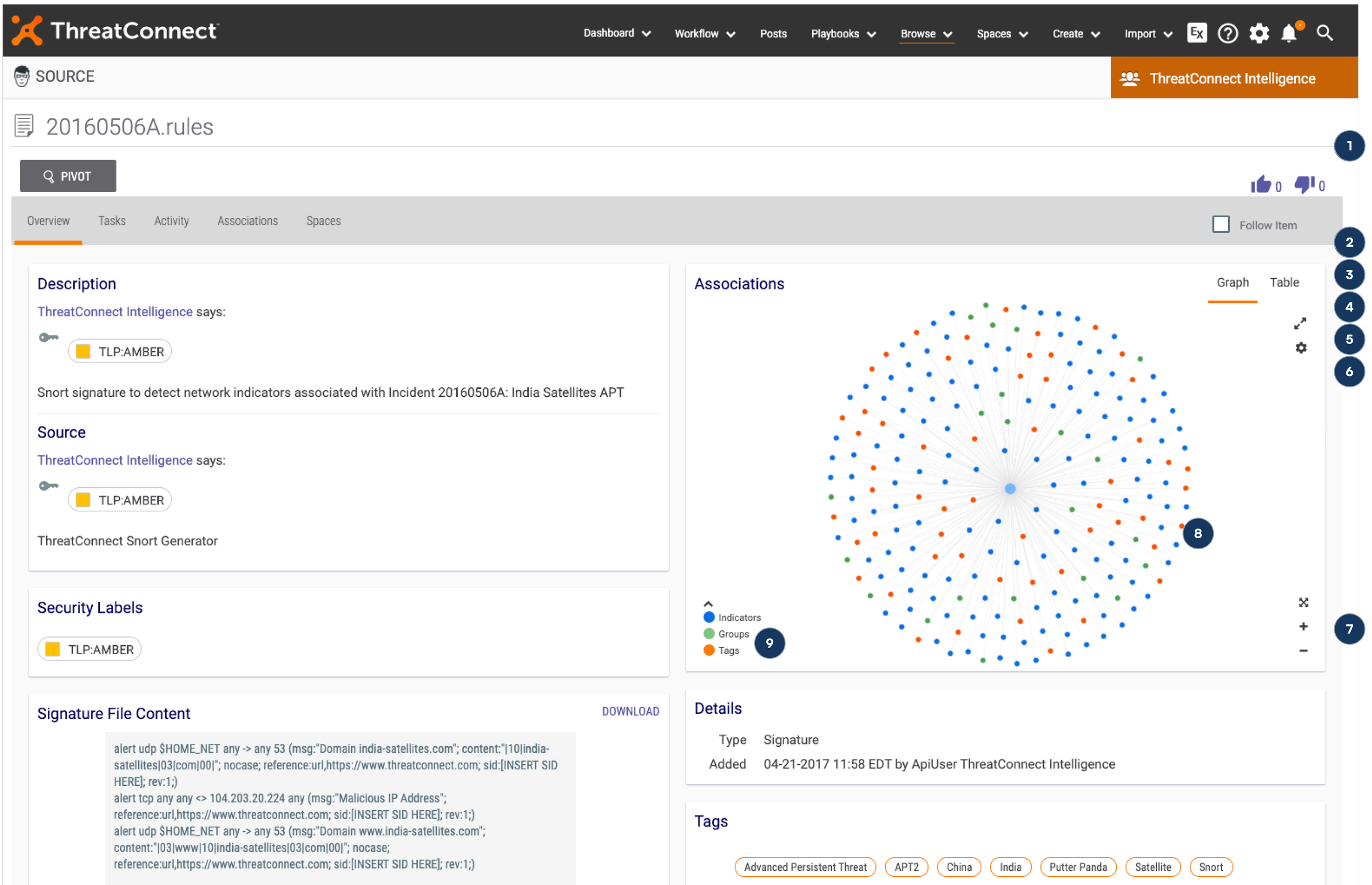
Visualization UX
I conducted competitive analysis of enterprise data visualization platforms, studying how Cambridge Intelligence handles large-scale network visualization as well as D3.js and Neo4j implementation patterns to inform scalable ux design.
User Flow Optimizations
Flow #1
Investigation Initiation: Starting from single indicator or alert, viewing intel from a case
Flow #3
Documentation & Sharing: Saving a graph view and sharing with a team
Flow #2
Relationship Exploration: Expanding connections to find related threats
Flow #4
Taking Action: Taking action on a piece of intel
Testing, Iterations, and Challenges
Usability testing
3 rounds of testing with 18 participants total
Task-based scenarios using realistic threat data
Measured completion rate, time-on-task, and error recovery
Iterations
I went through multiple rounds of iterations based of our usability testing and research. Some of the items that were changed over time were:
Bulk selection capabilities after 83% of users expected this functionality
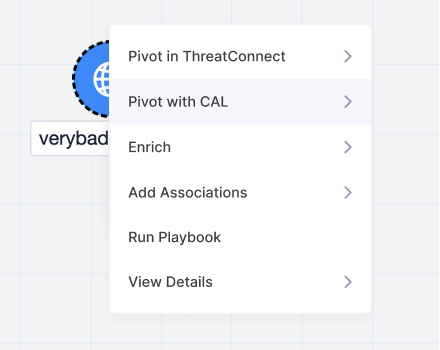
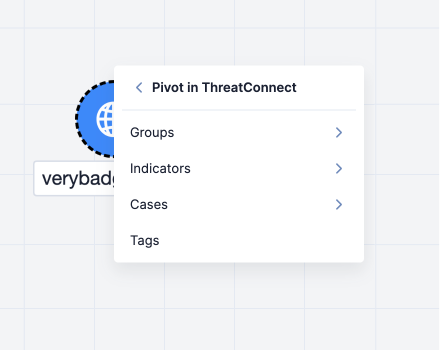
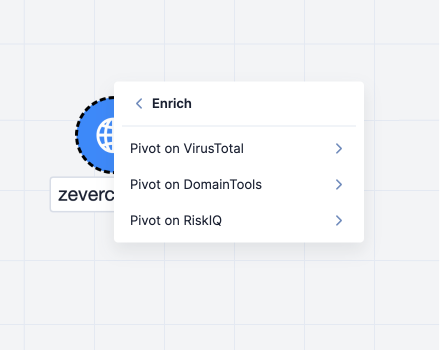
Changed the pivot pattern from a side bar search to a right click nested card
Implemented search after users struggled to find specific indicator when further along in an investing and results were long. Added pagination to handle load times.
Provided a way for users to control what columns were shown in the details side panel as analysts wanted to see specific data at specific points in the investigation
Moved button controls and concentrated at the top.
Challenges
The biggest challenge was validating early prototypes against limited data availability. I collaborated directly with the CAL data team, learning their data usage patterns while designing flows, which created a continuous feedback loop between design decisions and data insights.
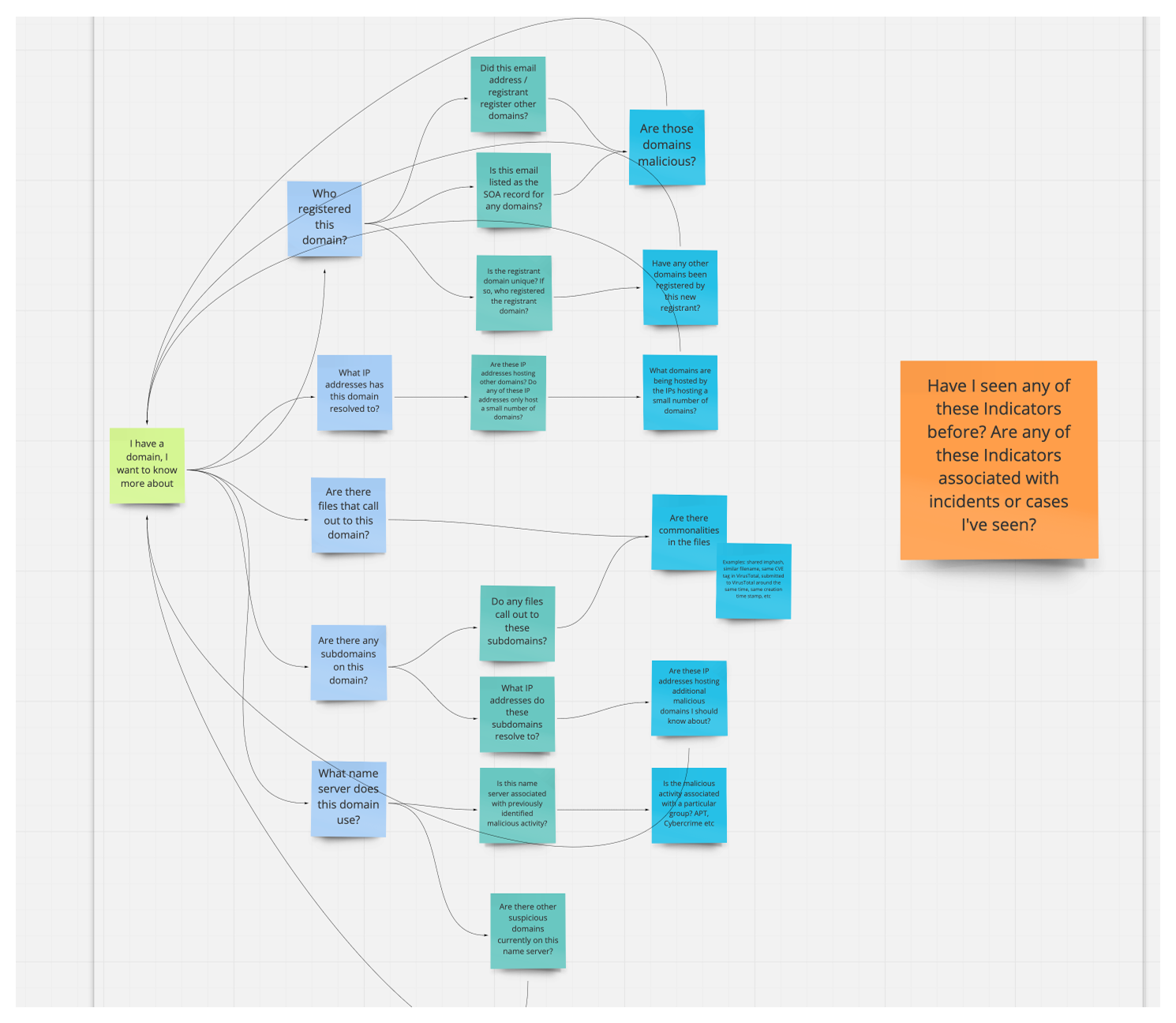
Pivoting on Data
Context-driven discovery vs. query guesswork
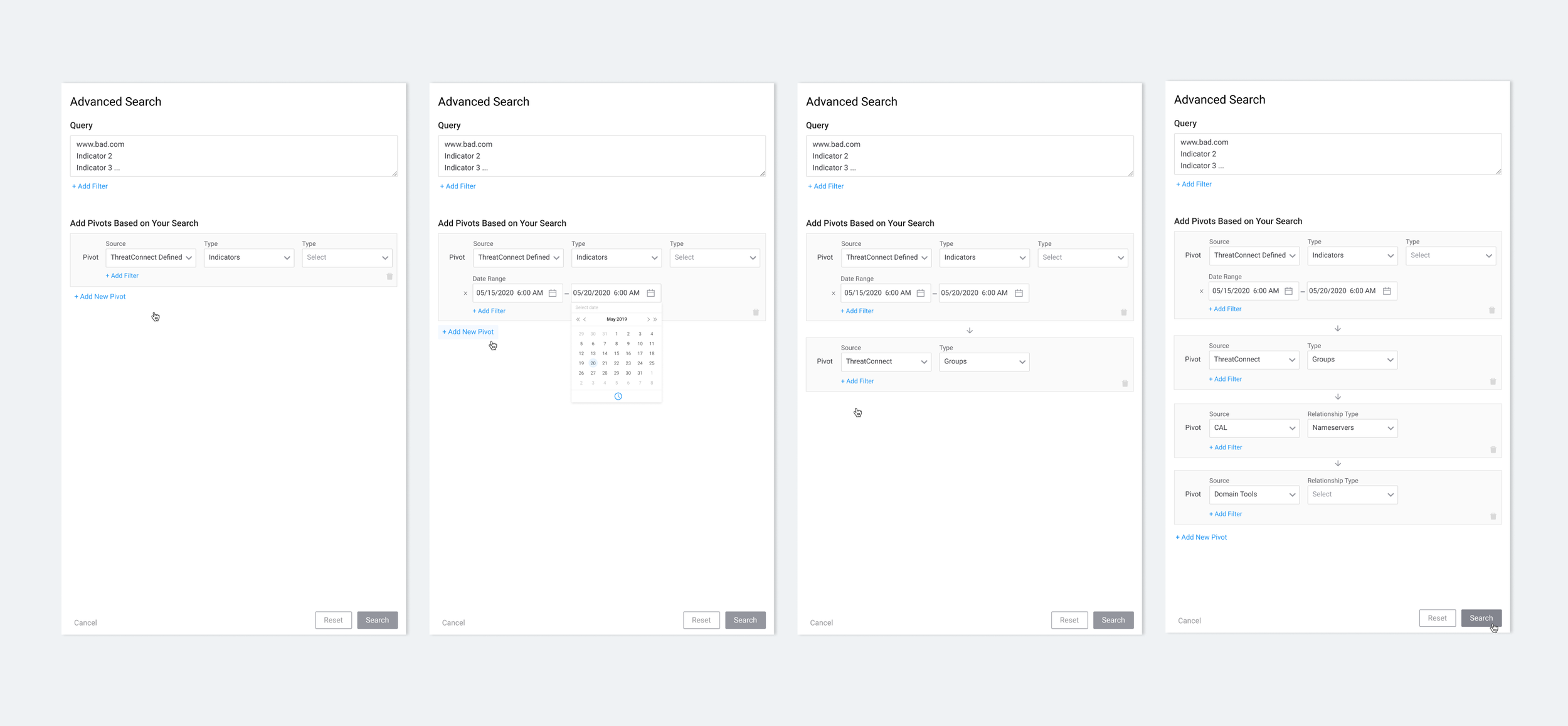
I originally explored different ways to pivot which included a side bar search, sql, and other patterns that could be supported with Neo4j. I found that as much as I wanted the query search to work, it brought up issues in my usability studies.
Cognitive Overhead - Analysts spend mental energy crafting queries instead of analyzing threats.
Syntax Barriers - Complex query languages require specialized knowledge, slowing down investigation flow
Assumption Bias - Analysts can only find what they think to query for, missing unexpected connections
Starting Point Paralysis - Without clear leads, analysts struggle to formulate effective initial queries
Example of the query and pivot pattern explored early on.
Single-node pivoting transforms investigation
Natural Investigation Flow - Pivoting followed intuition by letting analysts right-click to explore "what's connected to this suspicious domain" without syntax barriers, maintaining investigative momentum through continuous discovery.
Serendipitous Discovery - Single-node exploration reveals unexpected connections analysts wouldn't think to query, shows all available relationship types, and enables natural breadcrumb following from one discovery to the next.
Contextual Intelligence - Starting from known threat indicators provides immediate context that builds coherent investigation narratives through progressive disclosure while showing why entities connect, not just that they do.
Efficiency in Practice - 78% of analysts prefer visual starting points because pivoting delivers faster insights without query crafting overhead, reduces cognitive load to focus on analysis over syntax, and creates intuitive workflows that match natural investigation patterns.
Pivot options
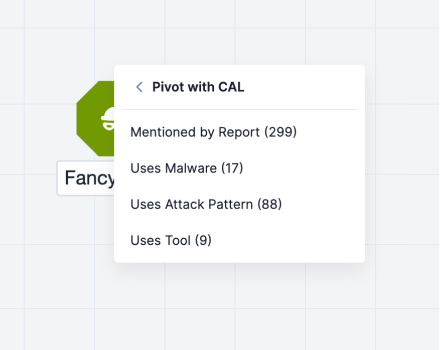
Pivot with CAL AI data
Pivot with TC Data
Enrich with third party tools
Example of the pivot pattern using CAL AI Data in the graph. Displayed is the node count for each pivot so analysts can determine the number of results returned before pivoting.
Final UI Design
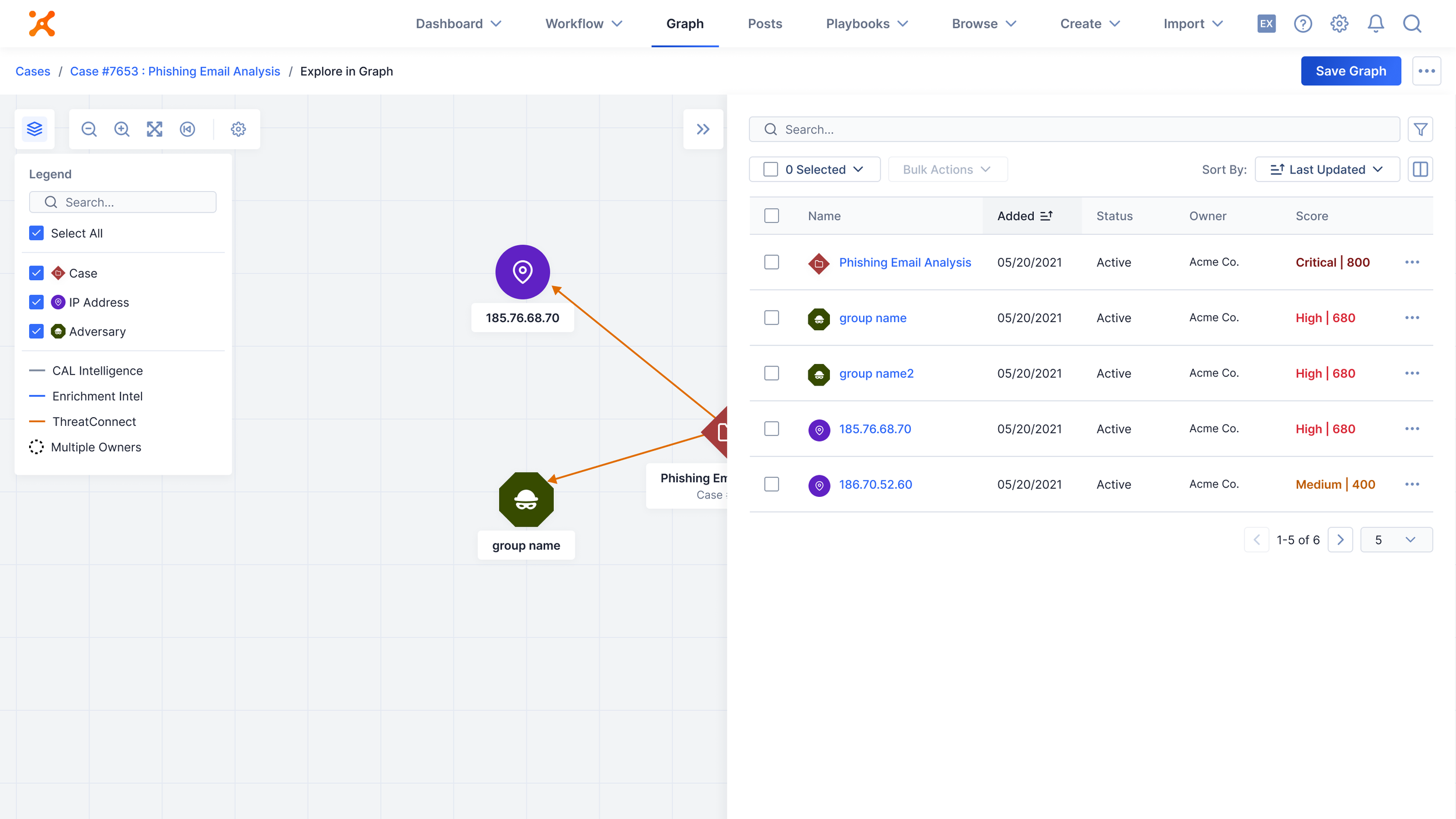
Full-screen graph experience
Expanded to full viewport for maximum data visibility, accessible via a new tab in the nav titled, “Graph”. Analysts can access from any piece of intel in the platform.
A legend for analysts to control what is viewed on the graph. Pairing back information is extremely important to reduce visual noise. Selecting a type of intel to show or not show, helps analysts narrow down their investigation.
Zoom and pan controls optimized for large datasets, with a zoom to fit and restore layout option if data becomes too spread out.
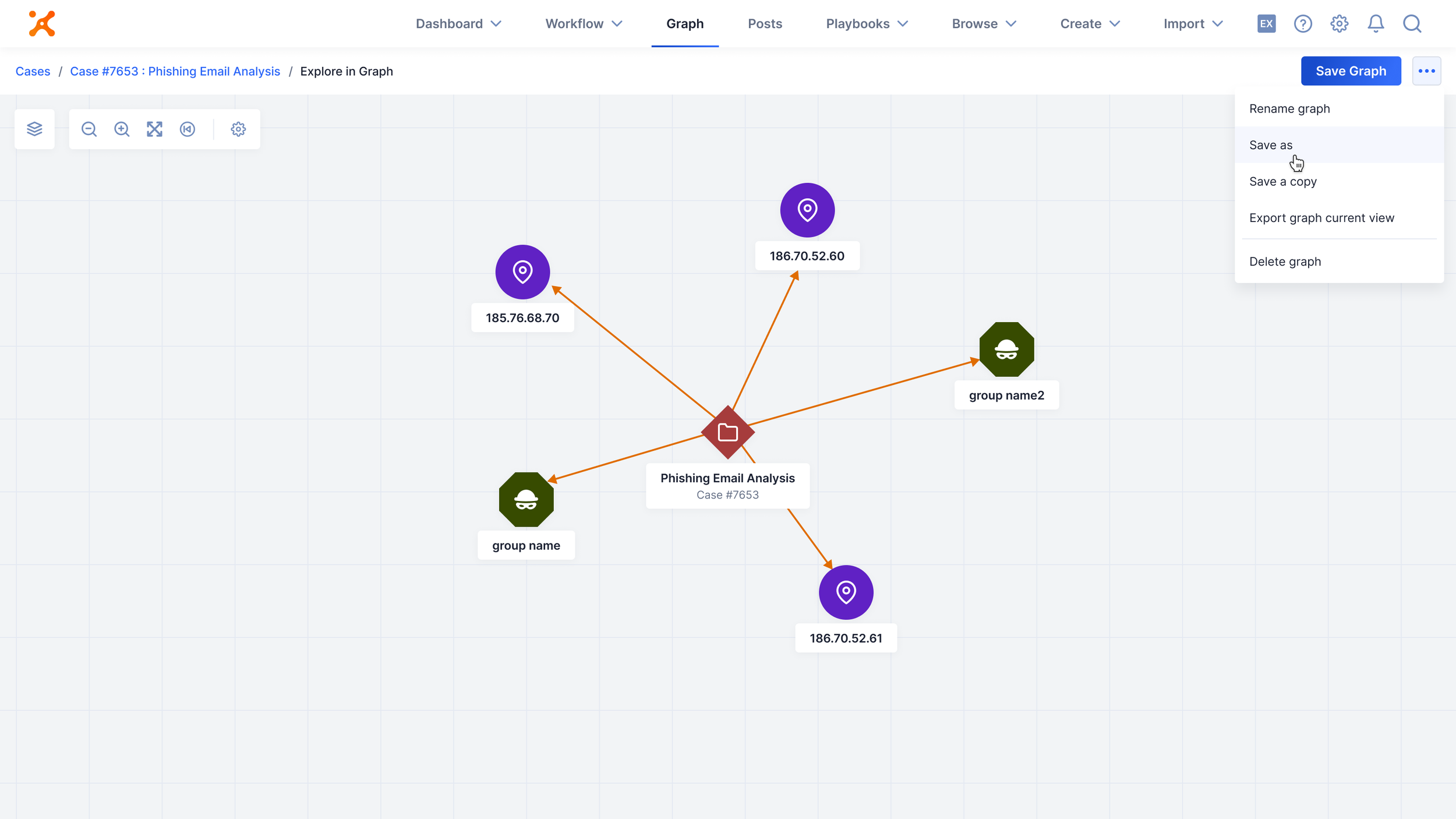
The final UI strategically positions controls in the top left, includes contextual breadcrumbs for multi-entry navigation, and places key actions like save and workflow operations in the top right for streamlined analyst workflows.
I created an interactive legend that serves dual purposes: onboarding new users to understand data meanings while enabling experienced analysts to filter out noise and focus on relevant threats. A collapsible right panel provides advanced filtering and bulk action capabilities for efficient intel management.
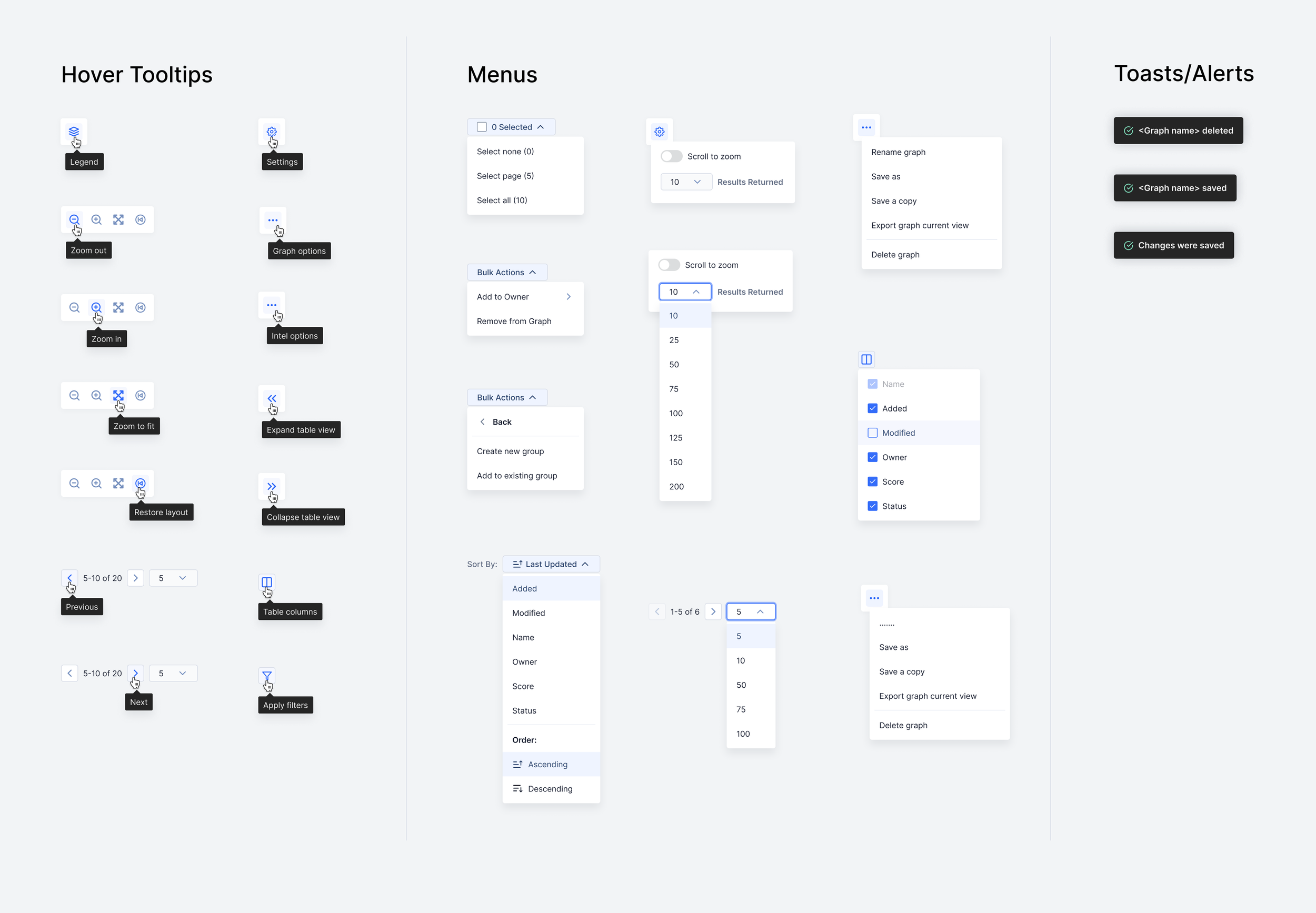
Tooltips and menus for the UI
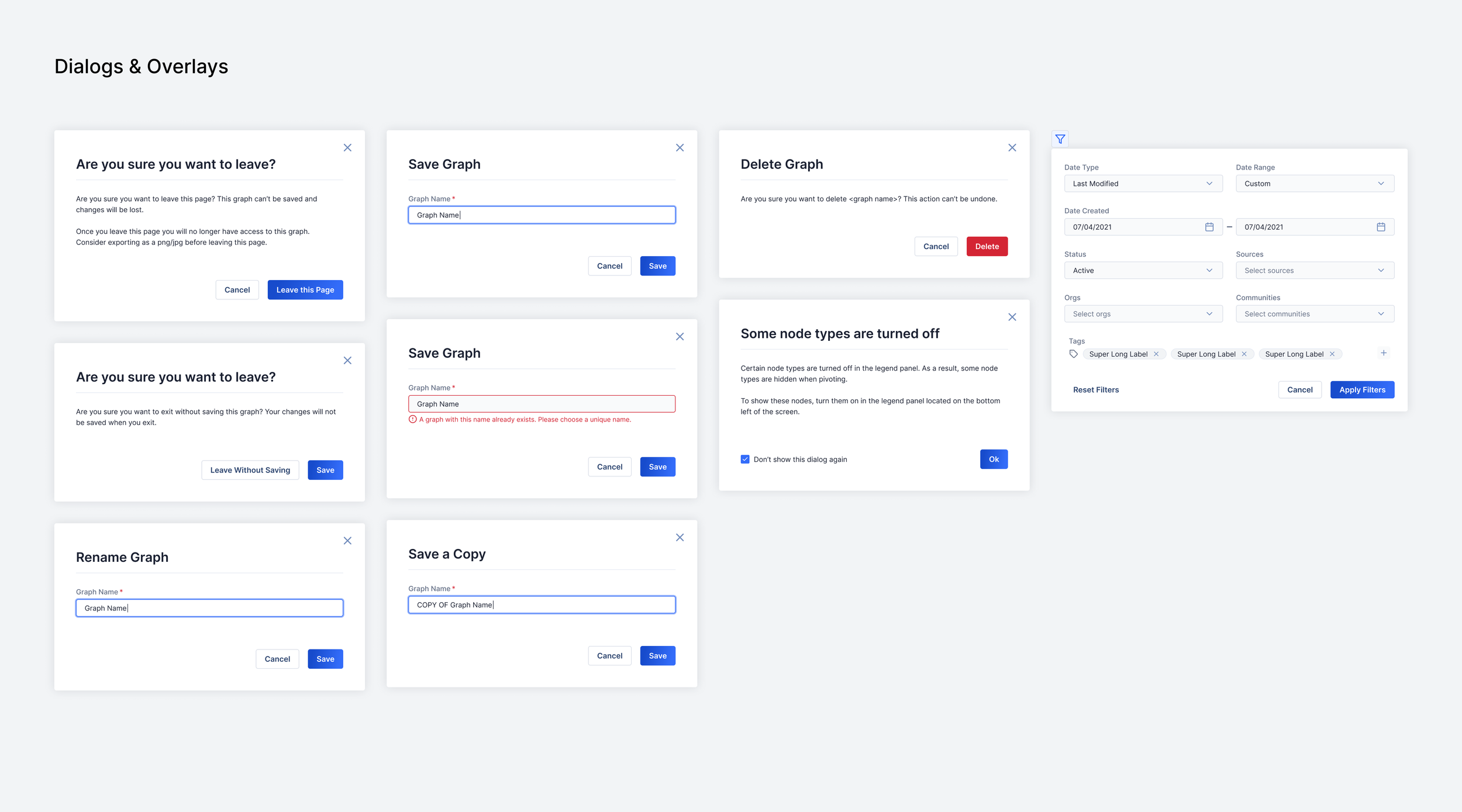
Dialogs and overlays including filters
Final UX Solutions
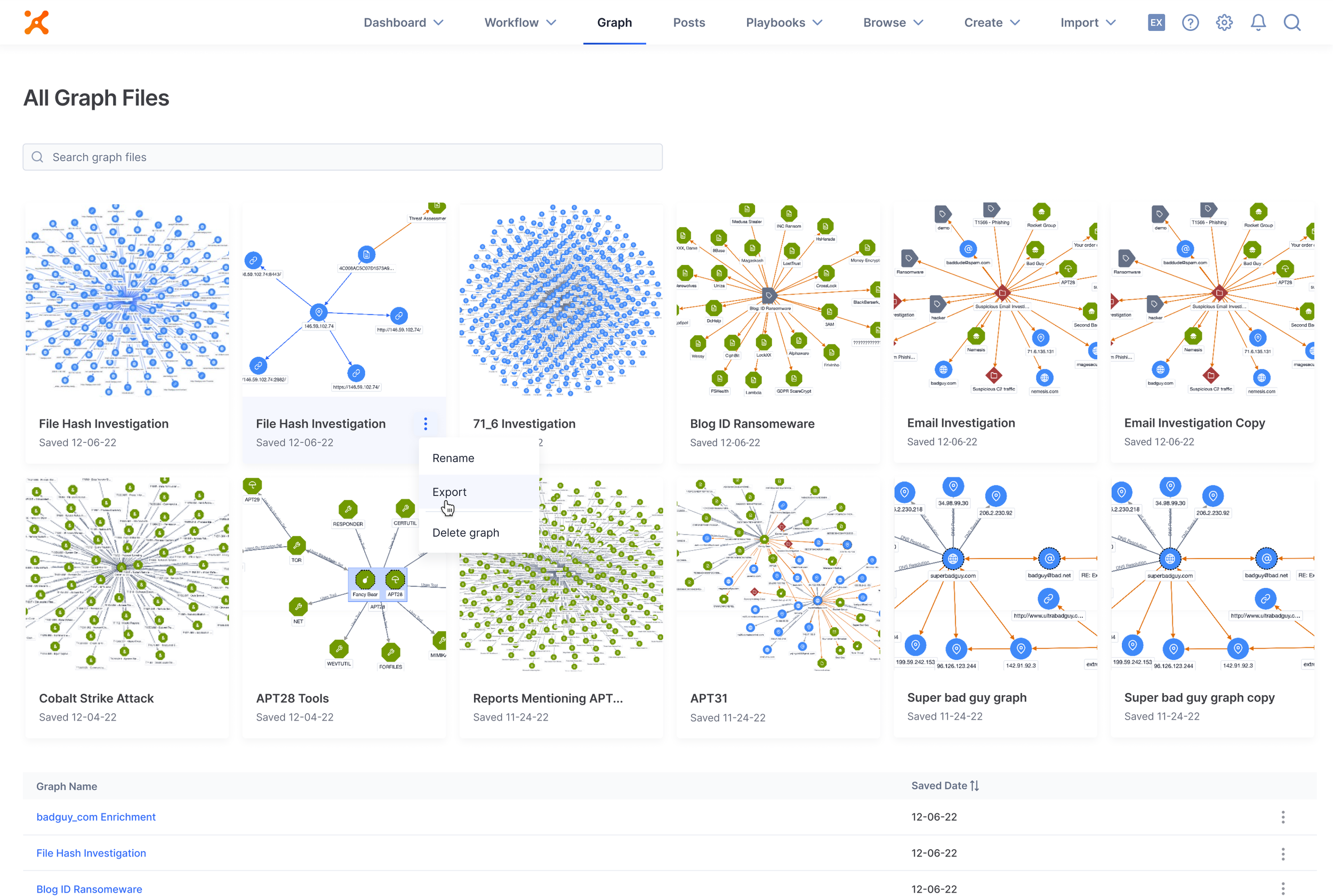
Overview the graph landing page with all graph files
Save or share a single view
View saved investigations from one place with most recent graphs located at the top with a snapshot view
Edit a previously saved graph so the graph evolved with an analysts investigation over time
Export to PDF/PNG for executive reporting and documentation
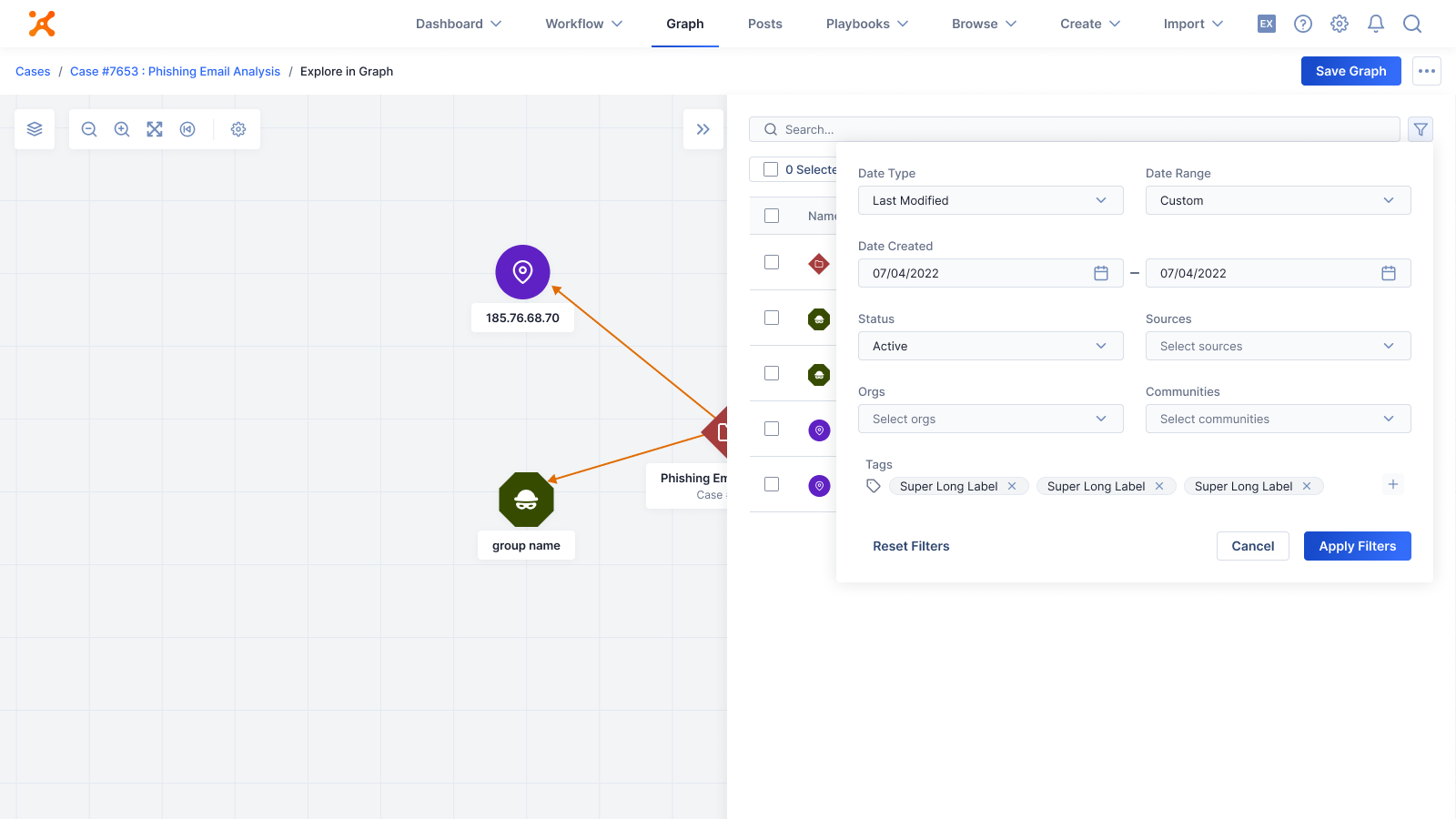
Search, filtering, and bulk actions
Boolean search capabilities across all threat intelligence data
Filter by confidence level, source, threat type, and time range
Bulk action capabilities enabling users to create cases, run playbooks, or assign owners directly from graph selections
Object removal capabilities allowing analysts to declutter investigations by removing irrelevant nodes through both individual and bulk selection
Advanced search filters available in the table view
Bulk actions as well as user control over what data is visible from the side panel
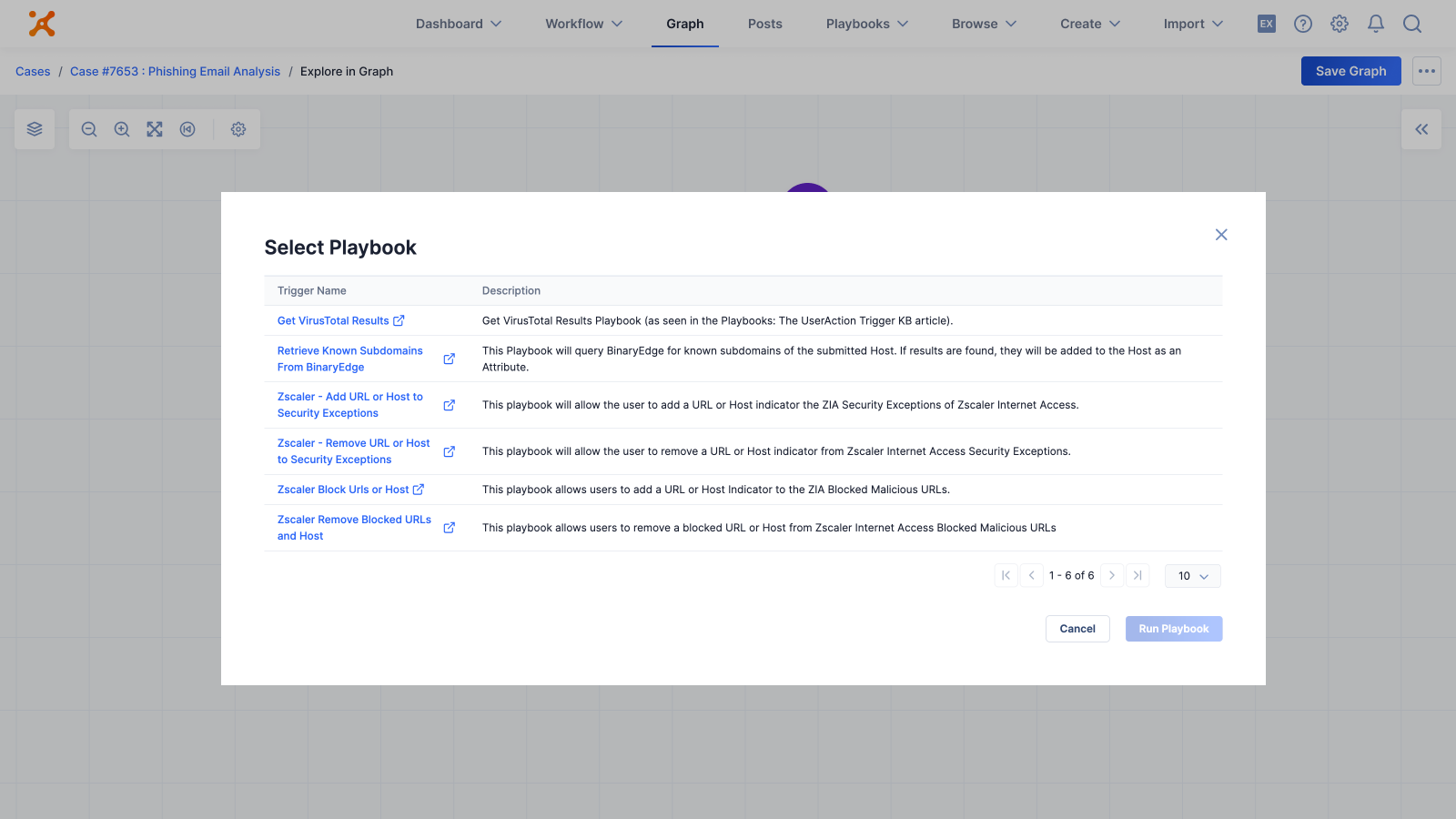
As a pivot option analysts can select a playbook automation within the graph
Connect to the ThreatConnect platform
View a case in the graph from the case view
Run a playbook for full automation on an indicator
Add associations to a piece of intel from the graph
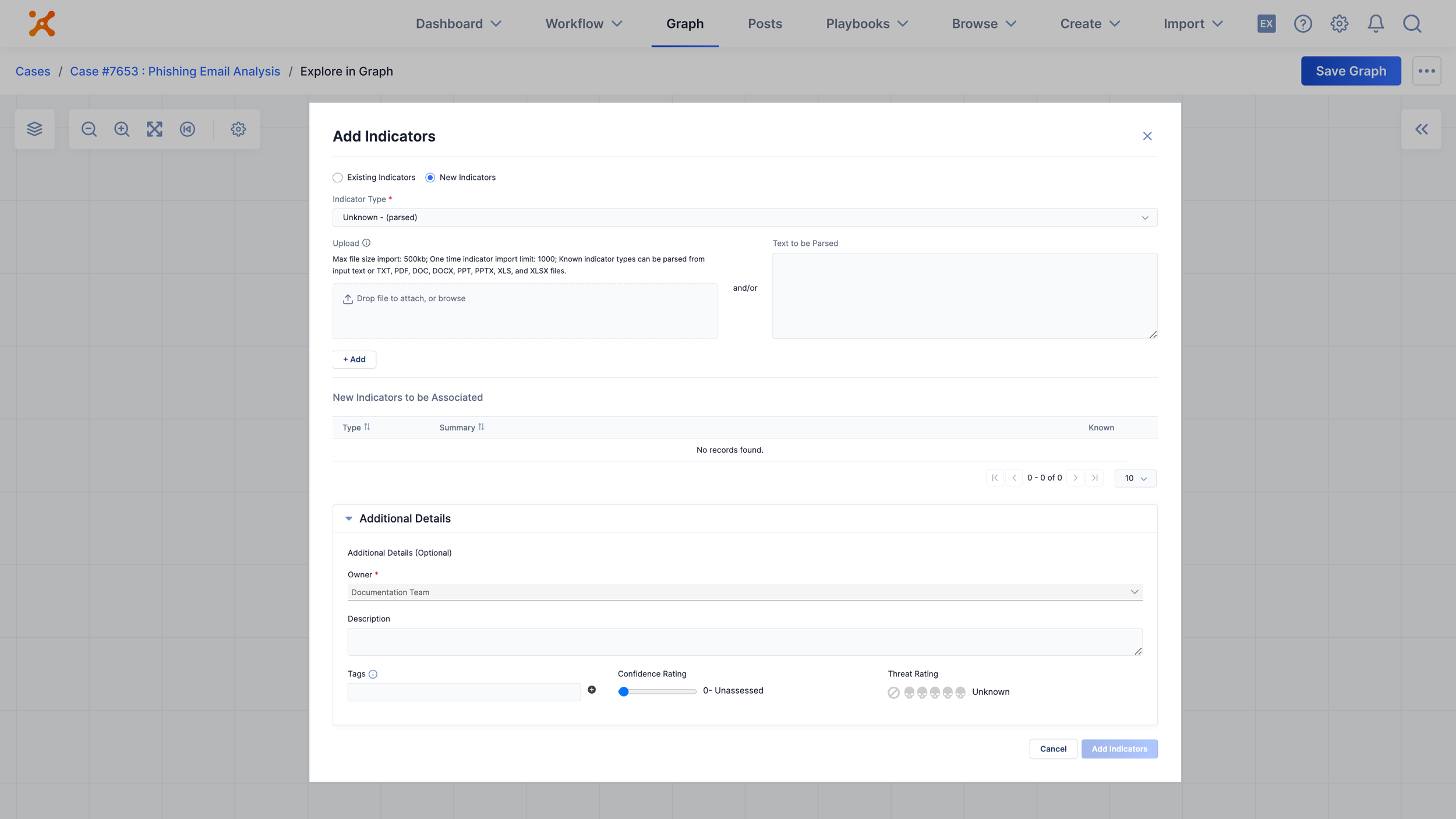
As a pivot option analysts can add new indicators/ data into the graph
Ability to save within the graph view.
Results & Impact
58% Increase
In monthly active users
$2.3M
In prevented customer churn through improved satisfaction
340% Increase
In session duration (8 to 35 minutes average)
40% reduction
In investigation time reported by enterprise customers
"The icon system is pure gold. We can finally distinguish between threat types at a glance.”
- Sr. Threat Analyst, Financial Services
"This actually has me excited and I'd prefer to use this to [competitor name]. The visual clarity is exactly what we needed."
- CISO, Fortune 500 Healthcare
"Investigation time cut in half. The AI insights help us focus on real threats instead of noise."
- Security Ops Manager, Tech Company
Industry Recognition
RSA 2022 Conference
Featured in 2022 for cybersecurity UX innovation
Gartner Recognition
In threat intelligence platform evaluation
Named Top 100
Innovative Cybersecurity Companies Of 2022 by Expert Insights
Global InfoSec Awards 2022
Won the Market Leader Security Software Award and Editor’s Choice Risk Management Award